Intrusion protection
Glossary protectionDefinition
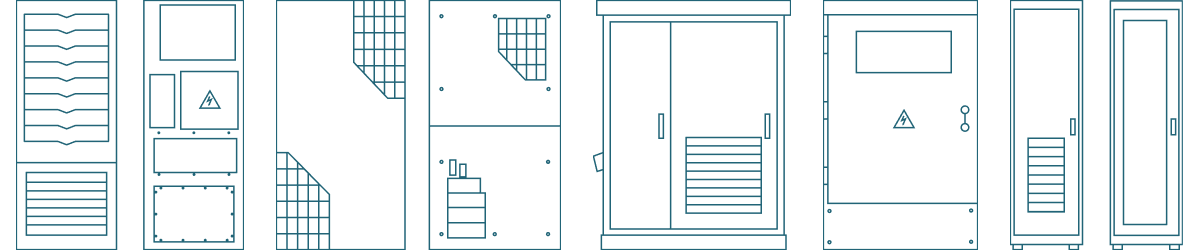
Intrusion protection is the combination of physical and electronic systems designed to detect, prevent, and respond to unauthorized access to an outdoor enclosure, server cabinet, or critical infrastructure installation.
Context
Intrusion protection is essential in telecom & connectivity, energy & grid infrastructure, oil, gas & mining, and defense & security applications where infrastructure is deployed in remote, unmanned, or publicly accessible environments. These systems protect against theft, sabotage, and unauthorized access that can disrupt operations.
Intrusion protection builds on access control (physical) and vandal-resistant design by adding detection and response capabilities. It is a key part of advanced enclosure design, ensuring both physical security and operational continuity in high-risk environments.
Technical insight
Intrusion protection systems combine structural security with detection technologies to identify and respond to unauthorized access attempts.
Key principles and components:
- Physical barriers and reinforced construction
Strong enclosure structures, often with vandal-resistant features, act as the first line of defense. - Access control integration
Systems are integrated with access control (physical) to restrict and manage authorized entry. - Intrusion detection systems
Door sensors and contact switches, motion detectors, and vibration and tamper sensors trigger alerts when unauthorized access is attempted. - Alarm and notification systems
Alerts can be sent to operators or monitoring systems when an intrusion is detected. - Remote monitoring and connectivity
Integrated with network systems for real-time monitoring and control, especially in distributed infrastructure. - Environmental and operational reliability
Systems must function under harsh conditions and meet IP Rating requirements to ensure consistent performance. - System-level protection
Intrusion protection safeguards:- DC power systems
- battery modules
- Network and control equipment
- Integration with enclosure and rack systems
Designed to work within:
Effective intrusion protection combines prevention, detection, and response into a unified security system.
Key advantages
- Detects unauthorized access attempts in real time
- Enhances security of critical infrastructure
- Reduces risk of theft and sabotage
- Supports remote monitoring and control
- Improves system reliability and uptime
- Complements physical and environmental protection
Applications
- Telecom base station enclosures
- Data center edge and IT infrastructure
- Oil, gas, and mining installations
- Energy and grid infrastructure systems
- Industrial automation systems
- Defense and security installations
FAQ
It refers to systems that detect and respond to unauthorized access attempts in enclosures and infrastructure.
Access control restricts entry, while intrusion protection detects and alerts when unauthorized access is attempted.
It is used in outdoor enclosures and critical infrastructure where security and reliability are essential.